Security of America's Computerized Voting Machines How hackable are American voting machines? It depends who you ask ...
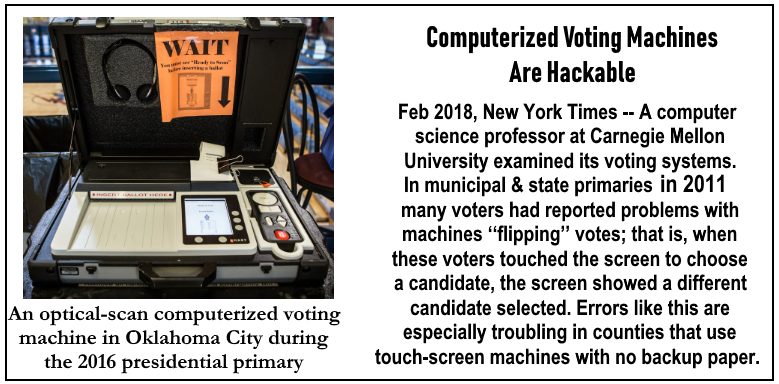
Oct 15, 2018 - Alex Halderman, professor of computer science and engineering at the University of Michigan testified about computerized voter machines' vulnerabilities in Congress and in court. In 2017 he told the Senate Intelligence Committee that states should move back to paper ballots. He said, “Often with voting machines, when you open it up, it’s not that different from a desktop PC or mobile device. The only difference is that it’s going to be 10 years out of date, or sometimes 20 years.” Myth of Hacker Proof Machines from New York Times, Kim Zetter 2-21-18, * -- In 2011, the election board in Pennsylvania’s Venango County — a largely rural county in the northwest part of the state — asked David A. Eckhardt, a computer science professor at Carnegie Mellon University, to examine its voting systems. In municipal and state primaries that year, a few voters had reported problems with machines ‘‘flipping’’ votes; that is, when these voters touched the screen to choose a candidate, the screen showed a different candidate selected. Errors like this are especially troubling in counties like Venango, which uses touch-screen voting machines that have no backup paper trail; once a voter casts a digital ballot, if the machine misrecords the vote because of error or maliciousness, there’s little chance the mistake will be detected. Concluding that the problem with the machines, made by Election Systems & Software (ES&S), was likely a simple calibration error. But the experts were alarmed by something else they discovered. Examining the election-management computer at the county’s office — the machine used to tally official election results and, in many counties, to program voting machines — they found that remote-access software had been installed on it. Remote-access software is a type of program that system administrators use to access and control computers remotely over the internet or over an organization’s internal network. Election systems are supposed to be air-gapped — disconnected from the internet and from other machines that might be connected to the internet. The presence of the software suggested this wasn’t the case with the Venango machine, which made the system vulnerable to hackers. Anyone who gained remote access to the system could use the software to take control of the machine. Logs showed the software was installed two years earlier and used multiple times, most notably for 80 minutes on November 1, 2010, the night before a federal election. The software, it turns out, was being used not by a hacker but by an authorized county contractor working from home. Still, the arrangement meant anyone who might gain control of the contractor’s home computer could use it to access and gain control of the county’s election system. It was just another example of something that Eckhardt and other experts had suspected for many years: that many critical election systems in the United States are poorly secured and protected against malicious attacks. experts say, attackers could also potentially use an IMSI-catcher or subverted telecom router to hack back into election systems and alter software to affect election outcomes. [..snip] The risk of someone hacking into voting machines via the modem is the problem, but vendors insist that the machines have protections to prevent this. Election officials also assert that routine procedures they perform would detect if someone altered transmitted votes or machine software. The top voting machine maker in the country, ES&S, distributes modems or modeming capability with many of its DRE and optical-scan machines. (Some states, including California and New York, require voting machine makers to not only remove communication devices from their systems but also eliminate communications capability from their software for security.) About 35,000 of ES&S’s newest precinct-based optical scanner, the DS200, are used in 31 states and the District of Columbia and can be outfitted with either analog or cellular modems to transmit results. [...] Not every polling place with embedded modems uses them to transmit results; however if it's available for use by an attacker it can be used. Richard Rydecki, Wisconsin’s state elections supervisor, says counties in his state decide individually whether to transmit election results via modem. Fred Woodhams, spokesman from the Michigan Dept of State said the same is true in his state. Experts still say even if a precinct doesn’t use its modems, having them embedded in voting machines is still a risk. Cisco, who makes the model of firewall used with ES&S election-management systems, announced a critical vulnerability in its devices that would let a remote hacker take full control of the firewalls and get at the systems they protect. News reports last week indicated hackers are already attempting to exploit vulnerable Cisco firewalls in the wild. ES&S says it’s working with customers to patch their firewalls and if they use the firewalls ‘according to recommended procedures; the vulnerability is mitigated. They can configure the firewalls to only accept connections from known and trusted IP addresses ‘‘and shutting off the system when not in use.’’ *Excerpted and adapted full original report from New York Times, Kim Zetter here More here Comments are closed.
|
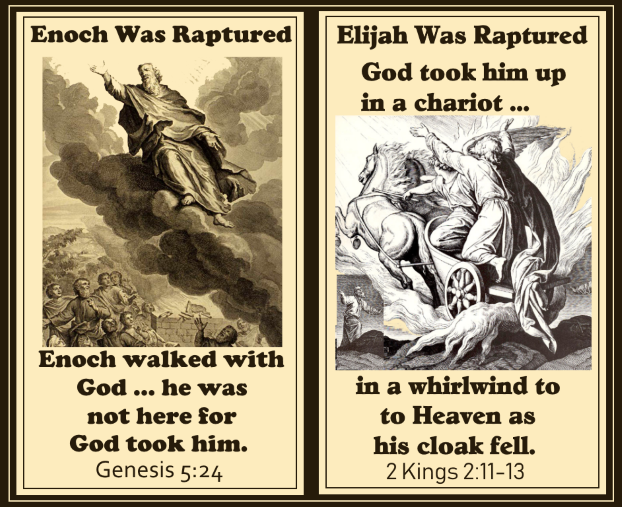
✝️ Titus 2:13 ♥️🙏
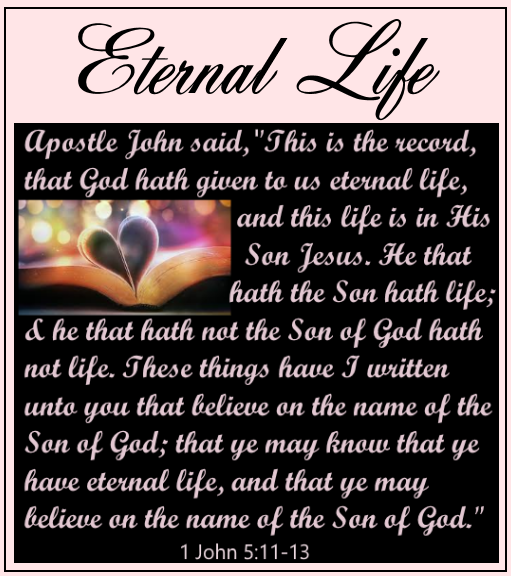
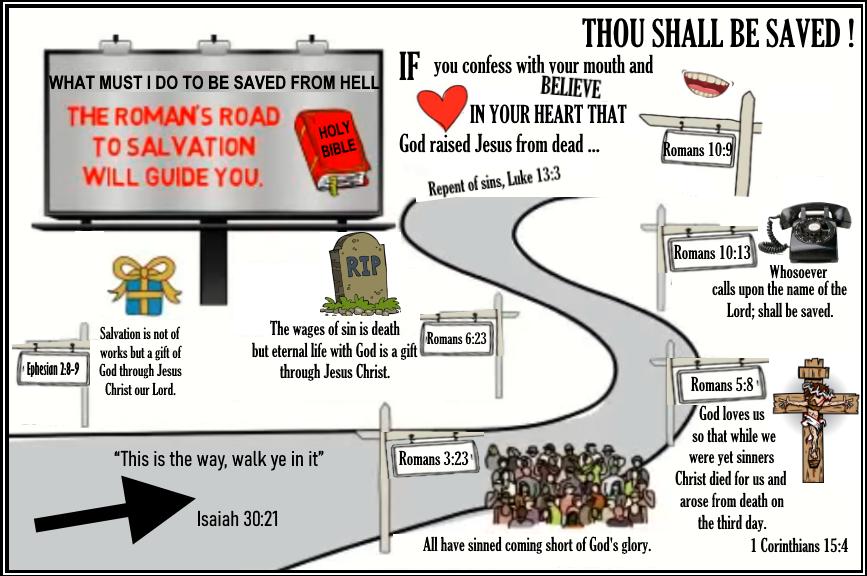
✝️🙏 Luke 13:3 ❤️
===
===
Index
All
Online Bible here
Exodus 20:2-17 God's Ten Commands
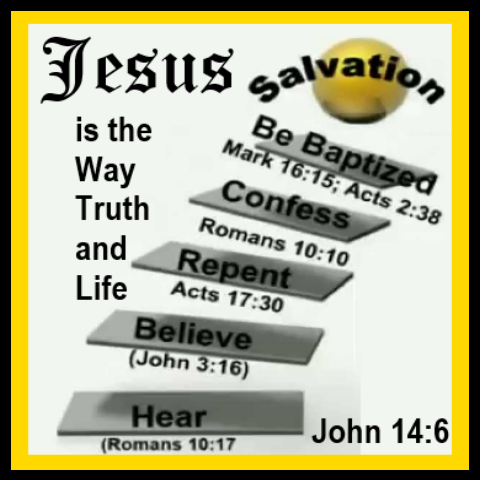
Jesus said: "Marvel not that I said you must be born again!' John 3:3, 7
Jeremiah 6:11 _____________
GOD'S STRONG DELUSION 2 Thessalonians 2:10-12 __________ Called, Chosen:
Matthew 15:13; Mark 13:20; Luke 20:35 John 6:37, 39, 44, 65 Hebrews 9:15 Revelation 17:14 We must obey God. Luke 11:28
FLY ME TO THE MOON SONG:
https://www.youtube.com/watch?app=desktop&v=pdJ0zMv4N4o Isaiah 26:3; Philippines 4:6
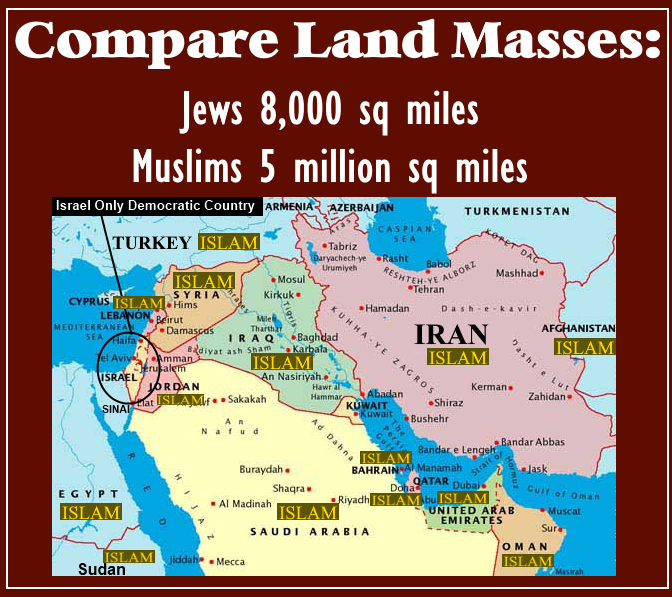
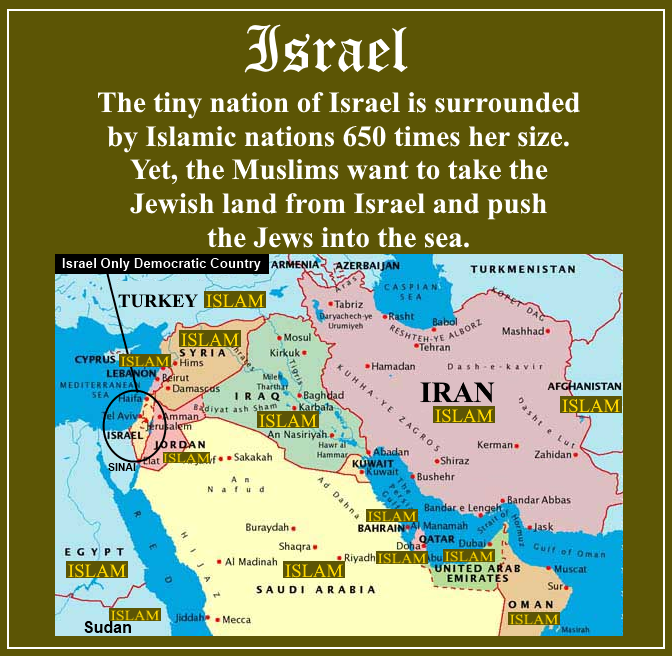
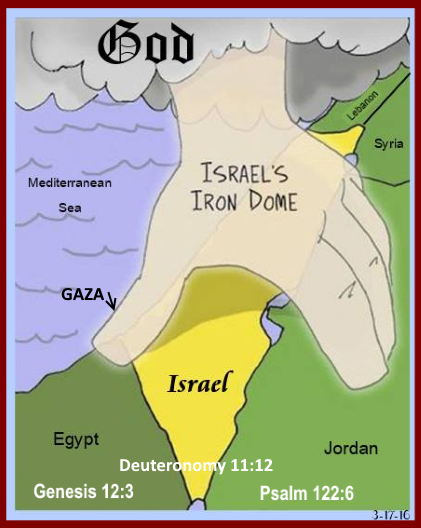
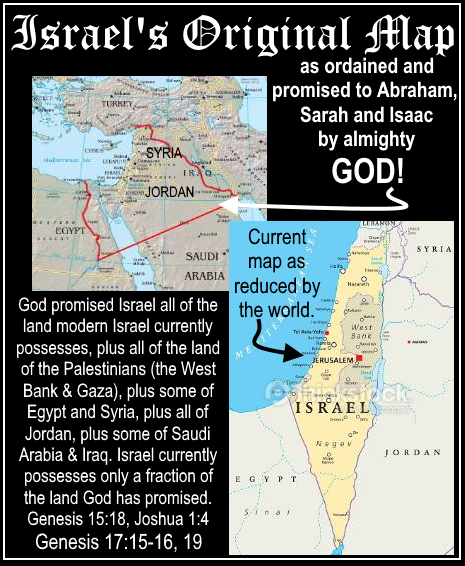
7-8-21-21, Israel has only 8000 square miles of land - the Muslims have 5 million. Yet, they also want the Jews land. Of all the nations of the world, the Lord chose the descendants of Jacob [Jews], not Ishmael [Muslims], to be His covenant people - the descendants of Abraham and wife Sarah. (Genesis 17:19-21; Malachi 1:1–5).
✝️ 6-8-20, Jesus is God; He came to save sinners. “For He [Jesus] Whom God sent speaks the words of God: The Father loves the Son & has given all things into His hand. He that believs on the Son hath everlasting life & they that believes not the Son shall not see life; but the wrath of God abideth on them.” John 3:34-36
✝️ 6-7-20, The Lord □ Jesus spoke from the cross first of forgiveness, salvation then of His Mother's care into John's hands. He spoke of being forsaken & then triumph as His task as human was complete shedding His perfect blood for the forgiveness of sins to all who repent believing in Him. His body was thirsty. And last of His reunion with the Father. Matthew 27:46; Luke 23:34, 43, 46; John 19:26-28, 30; Mark 15:34
✝️ 5-7-20, Sins □ Jesus Harshly Condemns; He said, “God knows our hearts: for that which is highly esteemed among men is abomination in the sight of God. V9 For all those who exalt themselves will be humbled, and those who humble themselves will be exalted.” [Pride] Luke 16:15, 18:9-14; Hebrews 1:8-9
Terrific Free Bible App for Cell Phone here
Psalm 91:3
Audio Bible
Jeremiah 4 Read the Bible
AuthorAnnette Greco-Meisner Archives
July 2024
===
Disclaimer: No violation of Copyright Law intended for any images or work presented - with no financial gain. U.S. Title 17 Code § 107 Section 106A-117 of the U.S. Copyright Law. "Fair Use Notice" Images and videos on this site may contain copyrighted material. That are made available for educational purposes only. ===
|
 RSS Feed
RSS Feed